Stay informed with free updates
Simply sign up to the Cyber Security myFT Digest — delivered directly to your inbox.
In my pantheon of heroes is American YouTuber Kitboga, who combats scammers with humour and guile. His army of granny bots embroil people who want their bank details in lengthy chats about knitting, while extracting information to trip them up.
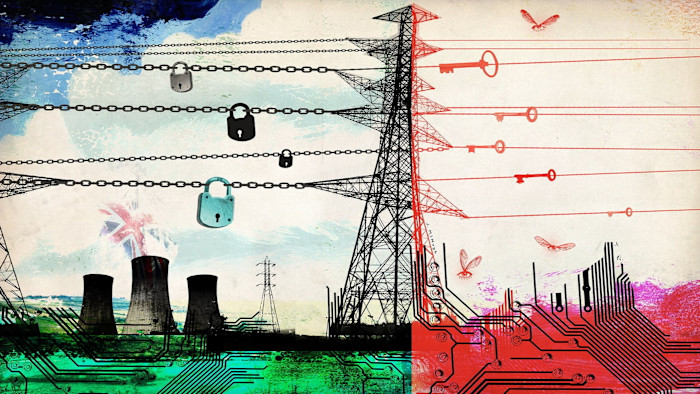
For all the wonders of our interconnected world, its vulnerabilities are stark. If people are still falling for the so-called “Nigerian prince” scam, how on earth will we ward off sophisticated sabotage by hostile states? The UK’s National Cyber Security Centre (NCSC) has warned that our collective ability to defend against cyber attacks has not kept pace with the threat.
Some of the menace is old-fashioned: industrial espionage, bribes to lawmakers, threats to dissidents like the Hong Kong exile Chloe Cheung. What’s changed is the apparent level of determination, from Moscow and Beijing in particular, to destabilise the west. China has hacked the emails of congressional staff in Washington in the past few months, while MI5 has issued an espionage alert to UK parliamentarians. In 2024 a ransomware attack by a Russian criminal gang on an NHS supplier called Synnovis led to the cancellation of hospital operations in London and an urgent call for blood donations. The same year, the FBI said that a Chinese state-sponsored hacking group, Volt Typhoon, had penetrated US energy, transport and communications systems.
If a war of attrition is being fought from a distance, by paralysing or impeding networks, then new strategies to combat it are needed. The blunt assessment of Matthew Collins, deputy national security adviser, is that “China’s espionage operations threaten the UK’s economic prosperity and resilience, and the integrity of our democratic institutions.”
Being vigilant doesn’t have to mean cutting ties. The west needs to co-operate with China on a range of issues, especially climate change and AI. The espionage game is a long one. The challenge is to co-opt more domestic actors into vigilance and to build partnerships with allies.
Two areas stand out. One is foreign interference. Here former UK prime minister Rishi Sunak’s 2023 National Security Act has created new offences while Sir Keir Starmer’s Foreign Influence Registration Scheme (FIRS) seeks to improve the understanding of hostile activity. Parliament’s Joint Committee on Human Rights has called for China to be designated under the enhanced tier of FIRS, partly to make universities take more seriously the possible risks of collaborative research. Ministers are wary of jeopardising relations. But the Collins assessment suggests it is urgent to signal security concerns to public authorities and businesses.
The other is the threat posed by the communications underpinning the “internet of things”. At the heart of many logistics systems, agricultural machinery, telecommunications and manufacturing lie electronic wireless components that collect and transmit data. The booming market for these cellular IoT modules (CIMs) is dominated by Chinese companies. In 2023, the UK’s Biometrics and Surveillance Camera Commissioner warned that the police and security services were vulnerable to spying from Chinese-made drones, CCTV and body cameras. Components have since been removed from sensitive sites, but it would be too expensive to rip them out of everything.
Security concerns have historically focused on “critical” infrastructure, such as nuclear power plants. But what security minister Dan Jarvis once called the “digital asbestos” is all over the place. Experts warn that a “kill switch” could bring traffic to a standstill or switch off home appliances.
It’s easy to scoff at hawkish types muttering about the CCP plotting from inside our kettles. But equally, it took the world a long time to wake up to the dangers of over-depending on one country for rare earths. It would be unwise not to anticipate that dependence on CIMs may pose just as great a risk.
The old strategy for managing risk was to separate the core from the periphery. That was the UK’s response when concerns were first raised about the role of Chinese telecom equipment maker Huawei in 5G networks. Australian premier Malcolm Turnbull took a different view: that 5G made the distinction meaningless. Australia banned Huawei from its 5G networks in 2018 while the UK focused instead on preventing monopoly, capping Huawei’s market share at 35 per cent. Then the White House banned the company and UK ministers had to change tack: telling mobile providers to remove all Huawei kit from 5G networks by the end of 2027, at a reported cost of £2bn.
Could the approach to the internet of things follow a similar path? Under the Biden administration, the US Commerce Department set a deadline of 2027 to remove all Russian or Chinese-linked software from vehicles, and 2030 for ending imports of linked hardware. Attention is now turning to energy systems. Turbines, smart grids and electric vehicles are part of a grey zone of potential threats. Last year, US experts discovered rogue communication devices in Chinese-made transformers, which they said could have been used to destroy the grid.
The obvious answer is to diversify. The Coalition on Secure Technology warns that Chinese CIM-makers enjoy a protected domestic market and that US, Canadian, Swiss, Japanese and Korean peers struggle to compete. Democracies will need to define trusted suppliers and probably subsidise them. This will have to be done on an international basis.
In one sense, this is simply a new iteration of the same old game. But as subterfuge ramps up, so must our own efforts to outwit it.


